
Though the Stuxnet cyber-attack which likely targeted Iran’s nuclear facilities may’ve begun as early as 2009, computer security experts have only this month published their full analysis of one of the most sophisticated and powerful computers worms ever developed, and what industrial damage it may’ve done.
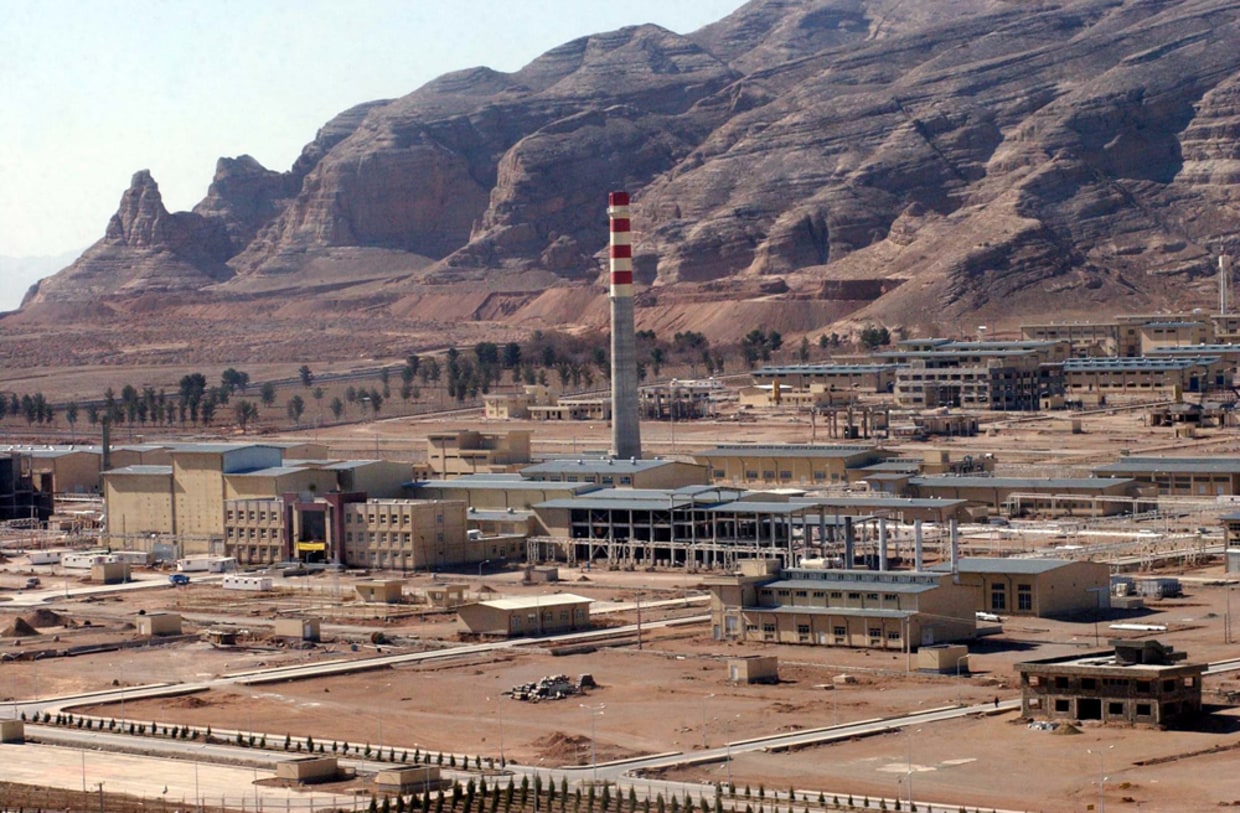
Stuxnet is malware likely designed to infiltrate Iranian (60% of computers infected were in Iran) industrial computers which controlled numerous automated processes in factory production cycles. The most likely target according to most experts consulted would be Iran’s Bushehr nuclear reactor complex, which last year was reported by Israeli media to have been sabotaged and faced extensive production delays. Since Bushehr is using Russian-supplied fuel not related to centrifuges or uranium enrichment, it seems unlikely they were the goal. But there clearly is some key industrial process likely targeted at Bushehr and the worm may’ve either destroyed equipment or corrupted a production cycle central to the reactor’s function.
By all accounts. the worm is so advanced, performs so many functions, and operates in such a complex fashion that it can only have been produced by the intelligence agency of a sovereign nation. We can imagine which nations would have the capacity to mount such an operation and the motivation to sabotage Iran’s nuclear program. The CIA and Mossad (or IDF military intelligence) spring to mind. My money is either on Israel and a shared operation mounted in some way by both countries.
IDF military intelligence has such a capability, Unit 8200, which analyzes intercepted communications and performs all manner of cyber-warfare tasks. A recent profile of the group described its operations in some detail though didn’t deal with the question of whether 8200 may’ve been involved in this attack. Forbes published this warm and fuzzy profile as well making 8200 out to be a real cool version of Silicon Valley.
This military unit performs a similar role in Israeli society to that of the Silicon Valley here. Since most Israelis serve in the army, this [8200] is where the techno-geeks among them gravitate. And when they exit their military service with their advanced technical training, they not only create commerical technology start-ups, they also continue developing products for Israel’s security apparatus. Such an 8200 alumnus founded Carmel Ventures, an Israeli venture capital outfit which funded Yuval Tal’s Payoneer, a U.S. company providing prepaid debit cards to its customers, who happened to be two of the Mossad hitmen who “hit” Mahmoud al-Mabouh in Dubai.
Since I don’t claim to be a computer security expert, but feel that Stuxnet is a very important development not only in and of itself, but also for the impact it will have on the Iran nuclear debate, I’m going to quote at some length from the recent technical articles about it in industry publications. It’s really fascinating stuff even for a layperson. Let’s start with PCWorld:
Researchers studying the worm all agree that Stuxnet was built by a very sophisticated and capable attacker — possibly a nation state — and it was designed to destroy something big…some of the researchers who know Stuxnet best say that it may have been built to sabotage Iran’s nukes.
…Last week Ralph Langner, a well-respected expert on industrial systems security, published an analysis of the worm, which targets Siemens software systems, and suggested that it may have been used to sabotage Iran’s Bushehr nuclear reactor...Bushehr reportedly experienced delays last year, several months after Stuxnet is thought to have been created, and according to screen shots of the plant posted by UPI, it uses the Windows-based Siemens PLC software targeted by Stuxnet.
…One of the things that Langner discovered is that when Stuxnet finally identifies its target, it makes changes to a piece of Siemens code called Organizational Block 35. This Siemens component monitors critical factory operations — things that need a response within 100 milliseconds. By messing with Operational Block 35, Stuxnet could easily cause a refinery’s centrifuge to malfunction, but it could be used to hit other targets too, Byres said. “The only thing I can say is that it is something designed to go bang,” he said.
…This is not something that your run-of-the-mill hacker can pull off. Many security researchers think that it would take the resources of a nation state to accomplish.
It is common for such malware to exploit a single weakness to infect a computer or system, but Stuxnet uses four separate vulnerabilities, which is unheard of for such worms. It also uses two forged digital certificates, which further indicates the highly sophisticated nature of the attack. It is important to note that Israel’s high tech industry has made a specialty of developing digital certificates. As one of my readers who specializes in IT wrote:
Public and private key technology (the basis of certificates) is indeed an Israeli computer specialty. The Weizman Institute in fact is the premier research university for such things.
What better country to forge a digital certificate than one whose techno hackers specialize in creating them? When you know a technology you also know how to exploit its weaknesses.
CNET’s report amplifies on Langner’s findings:
“With the forensics we now have, it is evident and provable that Stuxnet is a directed sabotage attack involving heavy insider knowledge,” he wrote. “The attack combines an awful lot of skills–just think about the multiple zero-day vulnerabilities, the stolen certificates, etc. This was assembled by a highly qualified team of experts, involving some with specific control system expertise. This is not some hacker sitting in the basement of his parents’ house. To me, it seems that the resources needed to stage this attack point to a nation state.”
Computerworld’s report quotes Symantec experts who have studied the worm extensively:
The Stuxnet worm is a “groundbreaking” piece of malware so devious in its use of unpatched vulnerabilities, so sophisticated in its multipronged approach, that the security researchers who tore it apart believe it may be the work of state-backed professionals.
“It’s amazing, really, the resources that went into this worm,” said Liam O Murchu, manager of operations with Symantec’s security response team.
“I’d call it groundbreaking,” said Roel Schouwenberg, a senior antivirus researcher at Kaspersky Lab. In comparison, other notable attacks, like the one dubbed Aurora that hacked Google’s network and those of dozens of other major companies, were child’s play.
Here they analyze in greater details the particular ways in which Stuxnet operates and the technical ambition and complexity required to create it:
Once within a network — initially delivered via an infected USB device — Stuxnet used the EoP [elevation of privilege] vulnerabilities to gain administrative access to other PCs, sought out systems running the WinCC and PCS 7 SCADA management programs, hijacked them by exploiting either the print spooler or MS08-067 bugs, then tried the default Siemens passwords to commandeer the SCADA software.
They could then reprogram the so-called PLC (programmable logic control) software to give machinery new instructions.
On top of all that, the attack code seemed legitimate because the people behind Stuxnet had stolen at least two signed digital certificates.
“The organization and sophistication to execute the entire package is extremely impressive,” said Schouwenberg. “Whoever is behind this was on a mission to get into whatever company or companies they were targeting.”
O Murchu seconded that. “There are so many different types of execution needs that it’s clear this is a team of people with varied backgrounds, from the rootkit side to the database side to writing exploits,” he said.
The malware, which weighed in a nearly half a megabyte — an astounding size, said Schouwenberg — was written in multiple languages, including C, C++ and other object-oriented languages, O Murchu added.
“And from the SCADA side of things, which is a very specialized area, they would have needed the actual physical hardware for testing, and [they would have had to] know how the specific factory floor works,” said O Murchu.
“Someone had to sit down and say, ‘I want to be able to control something on the factory floor, I want it to spread quietly, I need to have several zero-days,'” O Murchu continued. “And then pull together all these resources. It was a big, big project.”
…Put all that together, and the picture is “scary,” said O Murchu.
So scary, so thorough was the reconnaissance, so complex the job, so sneaky the attack, that both O Murchu or Schouwenberg believe it couldn’t be the work of even an advanced cybercrime gang.
“I don’t think it was a private group,” said O Murchu. “They weren’t just after information, so a competitor is out. They wanted to reprogram the PLCs and operate the machinery in a way unintended by the real operators. That points to something more than industrial espionage.”
The necessary resources, and the money to finance the attack, puts it out the realm of a private hacking team, O Murchu said.
“This threat was specifically targeting Iran,” he continued. “It’s unique in that it was able to control machinery in the real world.”
“All the different circumstances, from the multiple zero-days to stolen certificates to its distribution, the most plausible scenario is a nation-state-backed group,” said Schouwenberg
Symantec has also published a more technically detailed analysis of Stuxnet for the more adept among you.
Let’s step back and ask a few questions. While Stuxnet and other types of sabotage may’ve delayed Iran’s nuclear production and research, do we really believe that Iran’s scientists are so simple and naive that they would create only a single track for their work? Do we really believe this will cause any more than a temporary delay for them in developing their nuclear technology? No matter how damaging the worm is, no matter how impressive the technical achievement that brought it forth, it’s at best a stop-gap measure. As such, it doesn’t get at the root issue or the root way to resolve the problem which, once again like a broken record, I proclaim to anyone who will listen is a negotiated diplomatic solution.
Whatever Iran is trying to do cannot be stopped except by negotiation or war, leading to toppling the regime and replacing it with a West-compliant one (and good luck with that).
In regards to the latter option, if Israel deliberately used cyber-sabotage in order to mess with the minds and facilities of Iranian scientists, they may’ve coupled such an operation with a more deliberate one to bomb the facilities later. Such a two-pronged approach would make more sense from a military-intelligence perspective than simply messing up the production schedule of Bushehr for a year. But again, what do I know, I’m only speculating. Educated speculation by someone who has studied such minds at work for some time–but speculation nonetheless.
Paul Woodward, as usual, was one of the first bloggers to note a connection between Stuxnet and a possible U.S. or Israeli attack on Iran.





what do I know
thats says it all
why do you publish stuff you dont know
the issue is so much more complex and comprehensive
asking few amateurs around isnt going to help you
hundreds of brilliant brains and millions of combined
years have worked on something more comprehensive
then a regular guy like you can understand
why dont you stay on your regular antisemitic stuff ?
I know a whole lot more about this than you do fella. You should only have the level of expertise that the “amateurs” I quoted have.
It might be wiser to say that 60% of the known infections were in Iran. This software is only used in conjunction with Siemens PLCs, (system of standard industrial control and sensor modules on a rail programmed for custom control tasks.) There are, obviously far more of these in German and Spanish factories than in Iranian ones. There are also American and Japanese PLCs on the global market.
It is perplexing if it’s in more than one system if in fact it’s only designed to sabotage a specific installation, and needed to be installed from an infected USB stick as there’s no internet connection. PLCS are very universal tools, and all sorts of different installations use the functional group described for completely different things, so how does the hacker know what he is targeting?
I’ve spoken to people who think it is actually within the scope of a disgruntled Siemens employee, especially as no-one knows how much time was taken to do this. Half a megabyte of code isn’t a particularly large amount for an application using object-orientated programming languages. You’ll probably find that most of it is there to recognize a particular set of circumstances and comes from some sort of “AI” language, with the C++ bits to effect actions on the Siemens software.
This kind of controller is often used in moulds for advanced carbonfibre aircraft components, and a sudden change in temperature halfway through can destroy something which took a week to put into the mould and maybe two weeks to cure. This could seriously disrupt production of whatever the part is, especially if the factory had to be shut down while you work out what happened.
They’re not saying if this attempted to read back information on the curing profiles etc, which could well be technically important intelligence.
Another way of looking at it is: a way of punishing Siemens for supplying Iranian industry.
The nuclear plant everyone’s excited about almost certainly uses Russian technology in the critical areas. Although we don’t know if that’s a clone of the German technology.
Would be pertinent to know if the worm was already there when units shipped from Germany.
If I was the Germany Security service, I wouldn’t be assuming that this was solely aimed at and to do with, Iran.
If you read all of the articles to which I linked you’d find that the original infection happened through the Russian contractor working on Bushehr whose website is still known to contain malware & embargoed by some tech security companies. That’s probably where the infected USB device originated as well. YOu’d also know that the worm was designed only to infect 2-3 PCs at a time which would tend to limit the infection to the facility it was targeting & not bleed outside so the worm might be detected sooner. You’d also know that the first known instance of the worm goes all the way back to 2009. So the hackers had plenty of time to carry this out before they were detected.
The bizarre point here is that Bushehr is the reactor in Iran which is definitely *not* involved with a supposed Iranian weapons programme. Bushehr is the wrong type of reactor. The potential plant is at Natanz. I doubt that the Iranians really care that Bushehr was delayed.
We really don’t know what installation, or site (or, actually, on the facts, country) this was actually aimed at, and where it just happened to get, presumably by chance with a technician, wittingly or unwittingly, taking his favourite USB stick with him.
Perhaps someone sold a batch of infected sticks somewhere in Iran (or Germany) and the vast majority of them never met a PC connected to a PLC, so never did anything. We don’t know how narrow or wide the distribution was, because if no PLC, nothing happens.
Bushehr has been delayed for more than half my lifetime already…
If the equivalent Rockwell PLCs could also be targeted, there would be a short pause while the Pentagon’s relatively slow thought processes functioned, followed by the most spectacular panic, as these are used across the whole US manufacturing sector as well as many public utlilities.
General economic damage could be the name of the game.
OT : Have you seen this :
http://www.huffingtonpost.com/2010/09/23/israeli-leaders-slam-bill_n_737009.html
“Russian immigrants in Israel an obstacle to peace.”
Poor Yvet 🙂 though he is a Moldovian bouncer but I believe that he still have some love for Popov.
Here’s a serious hacktavist’s site who has a couple of blurbs about Stuxnet. He makes many of your same points but doesn’t make it out to be of mythical proportions. It could be cover for an embarrassment. Why would they be bragging about it if it was successful?
http://belowgotham.com/News.htm
More Details About Stuxnet – (2010-09-14)
“The fact that Stuxnet uses four previously unidentified vulnerabilities makes the worm a real standout among malware. …Add to this the use of Realtek and JMicron certificates…Stuxnet was undoubtedly created by professionals who’ve got a thorough grasp of antivirus technologies and their weaknesses, as well as information about as yet unknown vulnerabilities and the architecture and hardware of WinCC and PSC7.”
[…]
Stuxnet Update – (2010-08-07)
“Both Aurora and Stuxnet leverage unpatched ‘zero-day’ flaws in Microsoft products. But Stuxnet is more technically remarkable than the Google attack, Schouwenberg said. ‘Aurora had a zero-day, but it was a zero-day against IE6,’ he said. ‘Here you have a vulnerability which is effective against every version of Windows since Windows 2000.’
“To date, Siemens says four of its customers have been infected with the worm. But all those attacks have affected engineering systems, rather than anything on the factory floor”
“Most infected systems are in Iran, he added, although India, Indonesia and Pakistan are also being hit.”
If Iran is using Microsoft products to run nuclear systems they are too stupid to have a nuke plant. If the US and Israel doesn’t have anyone in there to know what they have, then how can they know about the damage they are speculating to have caused?
Apparently they are using Windows products of some kind as this was at least one of the security flaws through which they infiltrated the Iranian computers.
Israel likely does have some sort of inside knowledge of Iranian capability. Also, an Iranian deputy defense minister defected some time ago & told Israel about a lot of this stuff.
When using PLCs, it was hard to avoid some form of windows until recently, as the PLC makers only supported the hardware with windows software tools. Alternatives are available, now, but what’s being installed now is probably the fruit of several years work.
The small number of infections in Iran may reflect the number of Siemens PLC installations there. In continental Europe, the numbers are going to be almost beyond counting.
What sort of PLC a country uses tends to depend on whose modules the country’s leading electronics distributors are disposed to stock. They all do the same things, but you can’t really mix and match and once you start with Siemens, or Rockwell, you’re generally stuck with them for the life of the project, unless you want to dump all the work you’ve done up to the point you try and change.
Something that affects Siemens PLCs could damage the whole economy of a global region, an attack on Rockwell ones would damage a different global region.
Let’s see whether this stays local to Iran over the next year or so.
It’s known to have infected computers in Pakistan & India as well but the speculation is that the Russian contractor has clients there who got infected through malware on the Russian company’s website.
Why is that “nuclear plant computer screen” in English if it was developed and sold by the Russians to the Iranians? Plus, it is exclusively about water treatment so could be a domestic water treatment plant or even a wastewater plant.
I call “bogus”!
BTW, “If Iran is using Microsoft products to run nuclear systems they are too stupid to have a nuke plant.” – US plants make use of Microsoft Windows products although the critical safety functions have the logic burnt into silicon chips. There are fall-back systems that are hardwired (not digitized) that can shut the plant down safely.
Still, that could drop a lot of generating capacity off the grid even if it remains nuclear-safe.
Wouldn’t a nuclear power plant have a waste water system as part of its operations?
Of course nuclear power plants are water-cooled and so have several systems to purify water and cleanup waste. I’ve spent years of my professional life designing and building such systems.
My point is there is NOTHING about that screen shot that is specifically nuclear. Add in that it is English but built by Russians for Farsi-speaking operators and it looks fishy to me.
It is a photo taken inside the Bushehr facility. The original site which published it noted this as reported by the Christian Science Monitor.
OK, I’m willing to accept the word of the CSM. They are one of the few MSM I sorta trust.
So what? I’ll grant that it could be from the Iranian nuclear power plant.
I should apologize since my original questioning really didn’t affect the issue under discussion one way or another. It was a diversion from the thread and poor manners.
It is interesting in that the human factors engineering on display is waaay behind current US capabilities.
We need to reevaluate how we use terms like “cyberwarfare” in cases like this. Personally, I’d call it more of a preventive or defense system, with possibly the same purpose as an anti-missile system. Nothing happens until a clear and present danger is discovered, like a threat or launch. The fact that this “cyber defense” is sitting inside an enemy’s camp, is not an “act of cyberwarfare,” and even less so than Muslim zombies or sleeper cells in a Western country, who are not there to defend but to eventually do damage.
Regardless of the sources of this worm, it was apparently designed to act as a “cyber fuse,” which would shut down the aggressor’s ability to wage war, should that aggressor go too far from internal overheating (i.e. incitement). It is the free world’s way of containing Iran, or other rogue nuclear wannabees.
The only question that pops up is why this story was publicized outside of military circles. The malware researchers seem proud of their discovery, even posing for pictures, looking smug and proud. “Look at us,” they seem to be saying. But anyone who feels that Western nations need to control and leash pit bulls, the most logical thought is “Look at those jerks!” Nerds may know how to program code, but they’ve never been credited with showing foresight and wisdom. Those jerks have even been working at removing the malware!
Stuff & nonsense. Israel has made the judgement without any proof that Natanz is producing a nuclear weapon. This is not a defensive act. This is an offensive act. We know Israel has nuclear weapons. Is it legitimate then for its enemies to sabotage Dimona? But yr standards yr answer would have to be yes if you are not a hypocrite (which you undoubtedly are). The worm has acted before Iran developed a nuclear weapon. You simply don’t know what you’re talking about. The worm is gone fr. the system is was designed to harm. Still no nuclear weapon, the worm acted & it’s gone. You’re full of c(&p!
Tale about cyber-attacked Busher is contra-juives fiction provocative sleazy dirty lie addressed to understanding stupid fanatical population, produced by Iranian quasi specialists who are traditionally discovers the trace-of-jew as evil finger tape. The real criminal was – if it was – WINDJWS supplying for Nuclear Network control.
If I were an Iranian Investigating fellow I would interesting in this fact.
From other side this serenade may be song-to-world for demonstrate that Iranian genius may win even such snaky enemy as jüdische hohamim
A perfect example of Google Translate gone crazy. If you only told us what language you speak we could prob. do a better job of making you understood.