
Israeli media announced (and Hebrew) that Eliran Rosanes, 30, a disgruntled employee of Bank Leumi’s credit card unit (Leumi Card), stole data from 2.5-million bank clients, and was arrested. He worked as a customer service representative there from 2008-2013. In 2009, he was promoted to senior customer service representative, which offered him access to the customer database.
In 2013, he sought another promotion to a leadership role in the bank and it was denied. He then decided to steal the database and try to sell it or extort money from the bank after quitting.
He would listen to recorded conversations between bank representatives and customers opening new credit card accounts. He would listen for the customer to offer the security code and then locate the same account in the database. Combining this information allowed him to proceed to the next step in the fraud. Using a Skype account and a special application that disguised his voice, he would call the bank pretending to be the credit card holder and ask to change the mailing address. Once he’d done that he would call the bank and say the card had been lost or no longer worked. New cards would be mailed to the new addresses Rosanes and his partners in crime had provided. Then they used a motor scooter registered with false papers to travel to ATMs throughout the city, where they withdrew funds from the accounts they’d compromised.
He also used the cards to make fraudulent purchases making sure the amounts were under $75 so that it would be unlikely to arouse the suspicion of the credit card holder.
Later he, along with co-conspirators he’d known since childhood and whom police are calling “a bunch of nerds,” threatened to sell or expose the stolen data unless it paid $3-million.
Until this point, the case is a run of the mill extortion-credit-card-fraud scheme. But a confidential Israeli source tells me that the Shabak has been interrogating Rosanes and for the first few days he received the standard treatment, according to which he was denied access to his attorney. My source confirms, and this is where the case gets interesting, there is a security element to the charges (though he refused to elaborate further) against the suspect.
Yisrael Hayom alludes to this fact in this sentence from its report:
Additional charges were filed against him which are concealed under gag order…The secret [portion of the] investigation was highly complex and sophisticated, using advanced technological, intelligence and investigatory techniques with cooperation from the police negotiations unit.
The news articles note that he was captured in Thailand, where he’d become a fugitive. That’s an important clue to what Rosanes was likely doing there. You’ll recall that one of several alleged Iranian terror attacks against Israeli targets occurred in Thailand. It is a country that is neutral ground regarding the Israeli-Arab conflict. Israel operates there as well as many Arab countries. I find it highly likely Rosanes was peddling his data to an “enemy” Arab state or that such a country was collaborating with him in his extortion attempt against the bank.
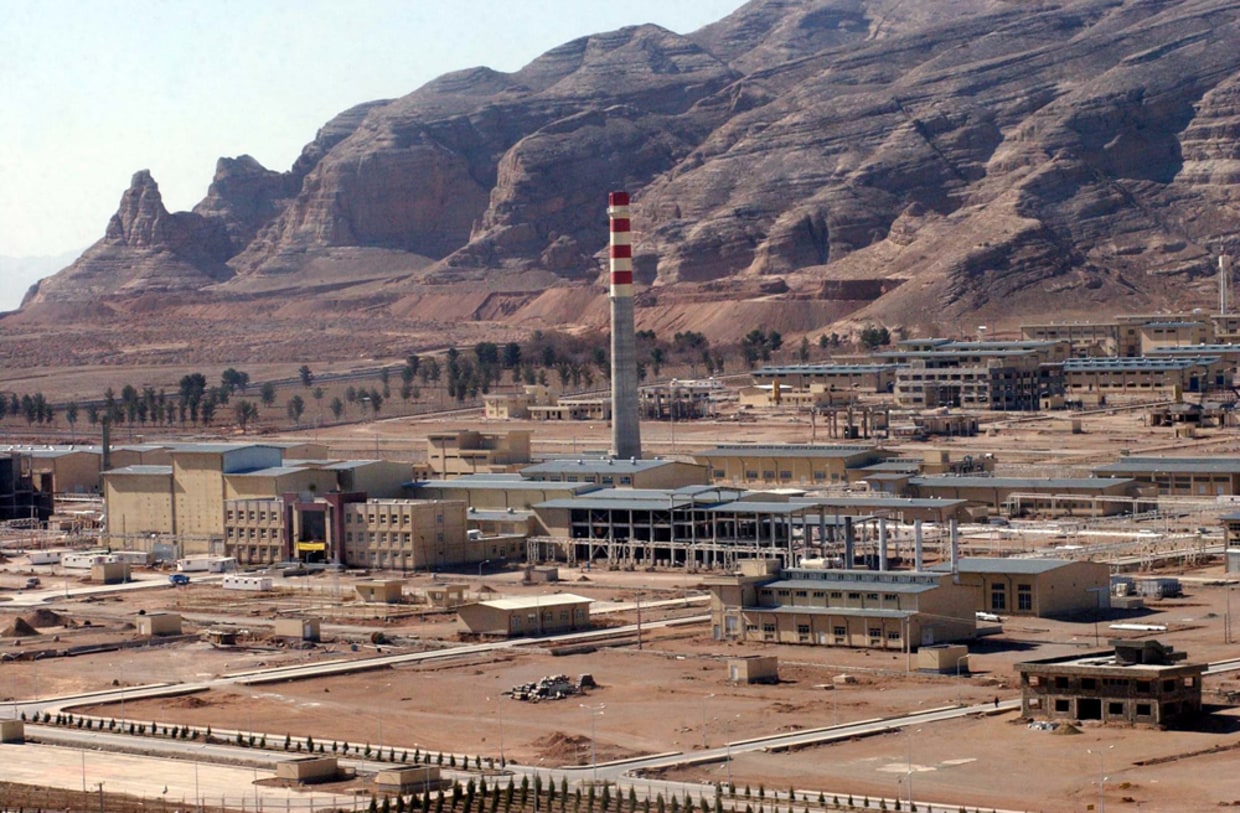
My guess is that it was Iran. Iran has reportedly engaged in various hacks targeting western and Gulf business and intelligence interests, including the U.S. Such attacks were in retaliation for Israeli-U.S. hacks of Iran’s nuclear facilities and other forms of industrial sabotage.
This certainly would be known to Rosanes. If Bank Leumi refused to pay, why not get the ultimate revenge? Sell the data to an enemy of Israel. That would hurt the bank and the State. Such a potential crime would certainly pique the interest of the Shabak and explain their involvement.
But again as I’ve written here many times before, how does an Israeli citizen trying to sell stolen bank data to a state hostile to Israel become a national security threat worthy of judicial gag order? Why doesn’t the Israeli public deserve the right to know the full story?
Finally, this has to be a huge embarrassment for Bank Leumi, which has just offered to pay a substantial fine to the IRS for allowing customers to shield taxable assets from the U.S. government. How does Israel’s largest bank permit the theft of data from 2.5 million customers by an employee? One hopes shareholders and bank customers are asking that question today.
NOTE: I published a new piece in Middle East Eye about the legacy of Stuxnet and other Israeli-U.S. cyber-weapons as seen in the recent Sony-North Korea hacking scandal. Please read and promote on social media.





How does Israel’s, population 8 million, 4th largest bank have a customer base of 2.5 million?
” I find it highly likely Rosanes was peddling his data to an “enemy” Arab state ”
What was an enemy State of Israel going to do with spoiled credit card information?
@ Figg: Leumi is Israel’s largest bank. My error.
But no one has said that 2.5 million customers is the entire database. It’s the size of the database he stole. There may be other databases. After all, he worked in the credit card unit & that’s probably the number of credit card customers the bank has.
As for peddling the information to other countries, who says the database was “spoiled?”
Bank Leumi knew, by way of the extortion plot, that the data had been compromised.
@ Figg: It didn’t know what data had been compromised. It only knew that some data had been compromised. Extortionists aren’t in habit of telling victims precisely which data they’ve stolen so victims can render the theft useless to the thief.
○ Bank Leumi and Lahav 433 cyber crime unit solved extortion scheme | Nov. 16, 2014 |
The suspect further threatened to sell the secret information to the highest bidder if his demands were not met, Ynet reported. Following the alleged threats, police’s elite Lahav 433 cyber crime unit launched a covert investigation into the case and determined that the suspect had been assisted by at least seven more people, six of whom had worked or were still working at Leumi Card.
The names of five of the suspects were released early Sunday morning: Ziv Darin, Avraham David, Assaf Mor, Elad Abulafia and Moti Shilon. The Magistrate’s Court in Rishon Lezion extended their remand by five days until Thursday. Six of the suspects, police said, hacked a main computer at a large banking corporation and copied sensitive files.
Gad Lior adds that cyber experts in Israel Police and the Cyber Authority also maintain a presence in Darknet for this very purpose, to expose cybercrime plots. The suspects were remanded on motzei Shabbos the eve of 23 Marcheshvan.
Richard – your imagination is amazing. You are squandered (???, מבוזבז) novelist. The only place that competes with the number of Israeli tourists with Thailand, and more specifically Bangkok and the Islands, is India. The leap you’re making is huge.
The court gag can be for any of many other reasons.
I never said there weren’t Israelis in Thailand. I said it was a good place for an Israeli hacker to go if he wanted to be in close contact with any number of Arab – Muslim states, since Thailand maintains good relations with such states..
I’ve written thousands of words on this subject in posts and my own comments here. I’ve done it not just once or twice but 10 or 20 times. I just don’t have the cheyshek to repeat myself.
Eliran Rosanes is the “Guardians of Peace” for Leumi Card (yes, the Sony Films thing was an inside job using the North Koreans as an accidental cover because the company and the Fibbies smelled an “international plot” that didn’t exist.) At least Rosanes gets to go to jail in that stylin’ Porsche hat; what is this, 1987?