God gave Noah the rainbow sign,
No more water, the fire next time!–African-American spiritual
Over the past few years, my blogging and freelance journalism has exposed Israeli national security secrets. I’ve revealed that Israel’s intelligence services along with those of Ukraine and Jordan conspired to kidnap a Gazan and bring him to prison in Israel, where he languishes without trial two years later. My reporting was the original basis of a 30-minute BBC radio documentary. I received top-secret FBI wiretap transcripts of conversations among Israeli diplomatic personnel undertaking a campaign facilitating war against Iran. I’ve exposed the identity of Jewish terrorists while they were under gag order and publication of their name was illegal inside Israel.
For all this, I’ve come under attack from the pro-Israel far right within Israel. Some of these attacks have involved computer hacking. I presume these are “script-kiddies” rather than government sponsored agents, but that line can be thinly demarcated. As you will also see, the line between a computer professional working for a multi-national corporation and a hacker can be very thin as well.
My website was brought down a few years ago by a Denial of Service (DOS) attack. Paypal once temporarily suspended access to my account. A company security representative told me an Israeli hacker was attempting to break into it.
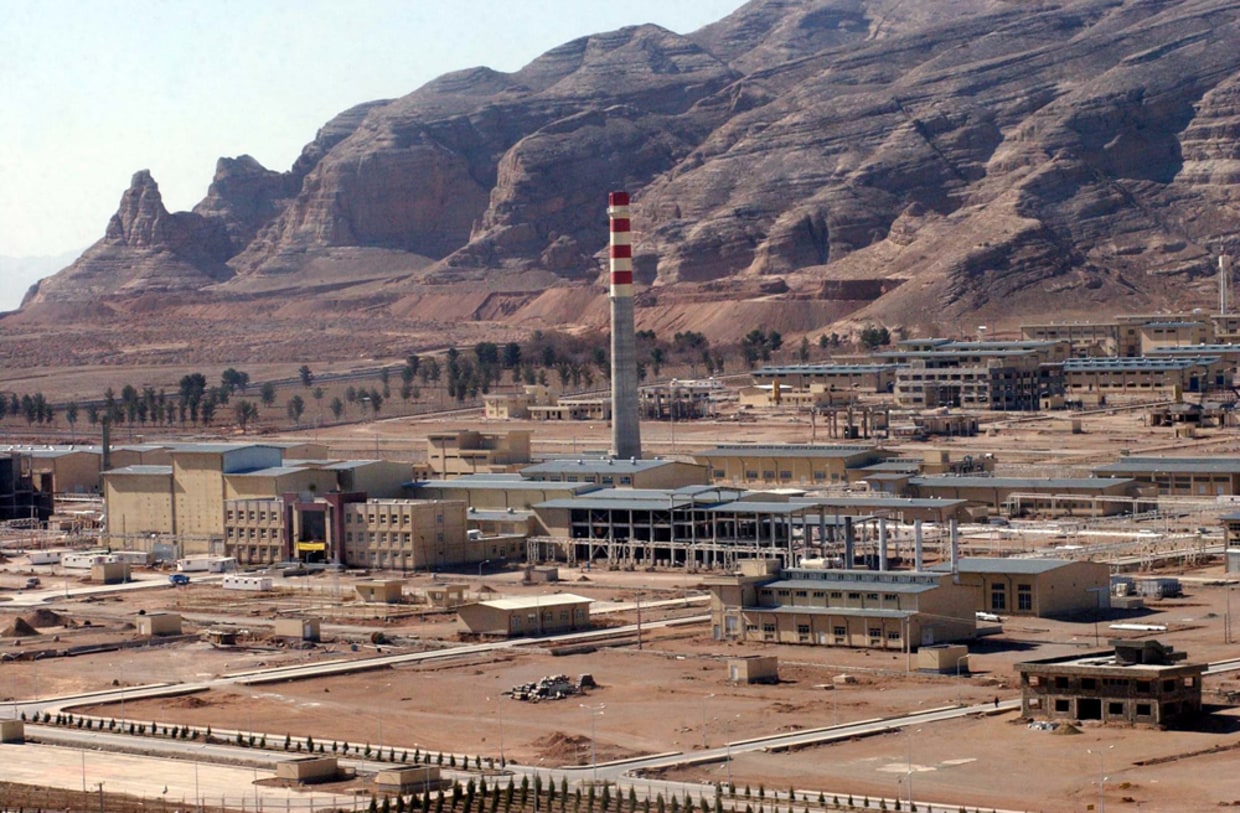
Last August, I published an Israeli government war plan outlining some of the military weapons systems to be used and the targets of an attack on Iran. It was meant as a sort of sales pitch to persuade reluctant ministers to support an Israeli assault. I was interviewed by BBC World Service (audio) and the story was picked up by Der Spiegel and other news outlets.
It’s no accident that three weeks later an Israeli hacker exploited a WordPress security weakness and took down my website. The hack happened in early September, as I was moving my site to a new host in order to provide more and better security. Ironically, this exposed my site to precisely the sort of hacking attack I’d hoped to avoid.

Dreamhost, which was to be my new host, had a One-Click installation which was designed to ease the transfer of WordPress websites to their server. Little did I know there was a security vulnerability that would allow an Israeli hacker to penetrate and take down my site.
I made the mistake of beginning, but not completing the installation. This allowed him to login to my site, create his own account, and hijack the main page, which took the site down for most of those attempting to visit. The rest saw a “proudly” waving Israeli flag with the message: “I Stand for Israel” emblazoned across the screen. In addition to thousands of readers finding my site down, there were substantial financial damages in restoring the site and moving it to a far more expensive host with superior security.
I’d switched my DNS (domain name servers) from my old to my new host before fully completing the transfer of my site. There are automated services that notify hackers when someone switches DNS servers. The hacker likely was monitoring my site for precisely the opportunity I’d inadvertently offered him. The combination of my WordPress installation being incomplete and knowing the DNS configuration allowed him to penetrate and deface my site.
UPDATE: In the paragraph below I wrote that David Lange had contacted the individual who attacked my website. In reality, it was a contributing author to Lange’s blog, Brian of London, who had these contacts and boasted about them in Lange’s blog.
The hacker also boasted about his exploit to a group of right-wing pro-Israel bloggers including David Lange of Israellycool and David Abitbol of Jewlicious. Lange admitted direct contact with the hacker, described the hack in detail, commended his exploits, and turned the attack into a right-wing pro-Israel campaign orchestrated possibly before, but certainly after the attack. Lange, who is a manager at SAP Israel, a subsidiary of an international technology company, has a history of fraud and sockpuppetry on social media sites. It was only one of the reasons I exposed his previously-shielded identity. Abitbol similarly praised the hack attack.
There was one thing the Israeli hacker hadn’t bargained for: in the course of reporting on Israel’s cyber war against Iran, I’d developed relationships with one of the world’s most prominent computer security labs, Kaspersky. They track the various cyber-weapons Israel and other nations use in their attempts to sabotage Iran’s nuclear program (though they take no political position on any of the political issues involved). Thankfully, they were also willing to help identify the attacker.
They produced a nine-page forensic analysis which offered strong circumstantial evidence of the hacker’s identity, identified the IP (internet protocol) address and ISP (internet service provider) used, when and how he attacked, and what damage he did. They were able to do this because the hacker himself made mistakes during his hack, including using his real e-mail address in creating the user account which defaced my website.

After Kaspersky provided this information, another researcher and I identified the purported hacker’s home address, phone number, employer and other personal information. I sought this information because I planned to report this as a crime under U.S. and Israeli law.
Kaspersky identified the most likely suspect in the attack as Semion Kras. He is an Israeli-Russian computer network administrator who works for IBM Global Services. The email address used to register his user account (semkras@gmail.com) at my site is his. The IP address (109.64.243.116) used for the attack is located in Rehovot, near Kras’ home in Modiin, Israel where he lives with his family. His ISP was Bezeqint, with whom I’ve filed a complaint. I also forwarded the Kaspersky report to the ISP. They did not reply.
The attack was reported to IBM’s security team which said they take such incidents very seriously and would investigate what their employee may’ve done and whether he did so while at work.
I spoke with a Kaspersky cyber-security expert who told me that all the information they discovered pointed to Kras as “the right person.” But the evidence does not necessarily constitute in and of itself evidence that could convict him in a court of law.
Usually Kaspersky will provide its reports to local or national police who will conduct their own investigation. They can secure ISP records that will offer further proof of the identity of the hacker. I’ve reported the attack to the FBI, but the amount of damage, though large to me, isn’t close to the normal threshold for them to take action. I’ve filled in by doing my own research.
Kras also started following me on Twitter (Twitter handle “semkras”) virtually on the day he hacked into my site. Among his Twitter followers he includes Bibi Netanyahu. His Twitter name is suitably entitled “Kaka.” His Facebook account includes “Likes” for an Israeli group “We’re All For Death to Terrorists,” Israellycool, and the IDF
Computer hacking is a crime under U.S. and Israeli law. Apparently, Kras believed his suspected hack would be clandestine and untraceable. Though hacking can often be done anonymously and with impunity, which is what Kras anticipated, he failed.
I called Kras at his home. I asked whether he spoke English so I could conduct the interview in that language. He said No. But later when I lapsed into English and conducted the rest of my discussion in that language, he had no trouble understanding me.
While he admitted that the email address used to register at my site was his, he denied he was the perpetrator. He claimed his e-mail account must’ve been hacked by the real attacker.
I asked him about the Twitter account that used the same “semkras” moniker as his e-mail address. He said he had no Twitter account. When I asked how someone would create an account using the same nickname as his e-mail address, he said it must’ve been someone trying to “spoof” his identity.
When I told him the Kaspersky report pointed to him as the likely hacker, he didn’t react indignantly. He didn’t threaten legal action. He didn’t hang up. All those responses might characterize an innocent party.
I asked Kras whether it was a coincidence that David Lange’s Israellycool was a Facebook Favorite of his (Lange had admitted communicating directly with the hacker). Kras admitted that he read Lange’s blog, but denied any direct contact with him.
The IBM computer technician denied having technical knowledge that would enable him to hack a website. I reminded him that as a network administrator who’d boasted publicly online about how to circumvent network server blocks for World of Warcraft players at work, he should have the ability to break into a website. He responded that hacking wasn’t his field and that he “didn’t do that sort of thing.”
He followed up with an e mail (written in excellent English) claiming he would offer me evidence that would identify the real hacker, but never did.
Since the attack occurred at 9AM Israel time on a weekday, it’s possible he was at work when the hack happened. Such usage of company equipment for illegal activity could put IBM in jeopardy. Since Kras published a manual for World of Warcraft video gamers wishing to play at work, it’s entirely possible he hacks during work-time as well. When I pointed all this out to him, it clearly hadn’t occurred to him that these were consequences he might face.
All of this might be of limited personal interest were it not that Israel is currently led by an ultra-nationalist Likud government that has engaged in a persistent campaign to destroy the last vestiges of democracy. This includes the government’s closure or threatened closure of TV and radio stations that air news segments critical of government policies; the arrest and imprisonment of journalists who expose military or intelligence misdeeds; the criminalization of speech including legal provisions to fine Israelis who advocate the BDS (Boycott, Divestment, Sanctions) movement; assaults on academic freedom including the threatened closure of the political science department at Ben Gurion University; criminalization of African refugees seeking asylum from civil wars raging in their countries; and violent assaults on political and ethnic minorities including leftist protesters, African refugees, and Israeli Palestinians. All of this on top of the ongoing Israeli Occupation of Palestine and the oppression of Palestinians and violations of human rights it entails.
In other words, the Israeli right-wing hacker who defaced my site was acting within a political environment giving free-reign to attacks on those espousing dissenting views. Free speech in Israel is a luxury offered only to the permanent right-wing majority and its allies. For all others, it’s open season. Kras knows that when he acts he isn’t merely engaging in a personal act, but that there is an entire pro-Israel blogosphere and society that endorses, either explicitly or tacitly, his deeds. That is why he turned to these blog allies to boast about his exploits.
There is one silver-lining in all of this: while cyber-attacks and other assaults on free speech may be countenanced by the Israeli right, there are still those abroad who find such behavior reprehensible. That’s why it’s important to expose such crimes and place them in the context of alarming political developments within Israeli society.
Israel is among twelve of the world’s fifteen largest militaries which have developed advanced capabilities for cyber-warfare. The IDF’s Unit 8200 is responsible for the most advanced worm created, Stuxnet, and others like Flame and Duqu, which sabotaged Iran’s nuclear program over the past year. Recently, Israel was reported to have destroyed a Sudanese weapons factory which manufactured munitions that were smuggled to Gaza. Local eyewitnesses report that Khartoum’s telecommunications system failed within an hour of the attack. There was no telephone, computer, television or radio available. The entire city was blacked out. This would indicate that Israel has perfected the means of crippling the communications systems and infrastructure of enemy nations.
The IDF maintains a series of technical high schools around the country which train students in computer technology and related fields. When they graduate, they are recruited to serve in units like 8200.
When graduates of IDF cyber-intelligence programs leave army service they take their expertise into the private sector and develop technology projects which further assist Israeli intelligence and cyber-capabilities. One example is the U.S. payment-services firm, Payoneer, which Mossad agents used to finance their travels and lodging while they plotted and carried out the Dubai assassination of Mahmoud al-Mabouh. Payoneer’s CEO is Yuval Tal, a former IDF special forces officer.
It’s a mistake to believe that such cyber-attacks and the damage they cause are limited to a few individuals or even a single country. With the increasing resort to such technology to undermine entire industrial systems or national infrastructure, this should be a matter of deep concern to the world community. It will be only a matter of time before cyber-war causes the same level of damage that conventional or even unconventional (WMD) weapons cause.
In that spirit, The American Interest published an essay, Hacking the Next War, which juxtaposed the traditional internet and the myriad benefits it’s offered to modern society, with the unplumbed destructive capacity of cyber warfare. The founding principles of the internet were openness and trust. Issues like security and abuse were after-thoughts, since the premise was that those who used the internet would behave with transparency and good intentions. In many ways, the founders believed fundamentally that human beings were good. The beauty of these concepts is that they’ve produced extraordinary amounts of commercial wealth along with an outburst of invention and creativity that have enriched modern civilization:
Today we live in a world linked by “cyberspace,” a word…[that] stands for the completely man-made substrate we all share intimately on our smart phones, tablets and desktops, and that pervades the operations of banks, airlines, electrical grids and even manufacturing plants. It stretches under and into all the relatively instantaneous (and profitable) communication, cooperation and coordination that sustain our modern quality of life. So much modern wealth now relies on cyberspace that, increasingly, groups and nations are beginning to fight in it and over it as well.
…Globalization and cyberspace are deeply intertwined…Successive waves of globalization gradually transformed classic independent, territorially buffered…states into openness-dependent, wealth-obsessed and war-averse…democratic commercial trading states. Nations from the European Union to South America to the democratic Asian tigers act more like the city-states of long past than early modern…states capable of going to war to defend their interests. Their political leaders focus on facilitating aggressive trading benefits and forging international rules of exchange, not on preparing for destructive conflicts. Since World War II, they have built, institutionalized, and lived by openness—to global commerce, finance and knowledge flows. These states now internally and legally enforce shared, relatively compatible rules on their…groups and citizens. Even when international members violate the rules, no one threatens war to recoup material damages. Globalization has domesticated, as well as made more porous, the warring nation-state into a relatively defanged modern city-state dependent on the civil behaviors of other states and their citizens in the international system.
In his piece, Chris Demchak notes the rise of what he calls “bad actors.” Those who see the web as a way to make a quick buck, or to advance an ideology. But the author, a professor at the U.S. Naval War College, makes a surprising assumption regarding the identity of these disruptors of global commerce. He presumes that they are largely individuals or organizations working for money or power or even for the hell of it. But rarely does he address the fact that the most dangerous actors, due to the potential for damage they can inflict, are states themselves and their agents. In fact, the author downplays the impact of nation-states and calls upon the U.S. to focus on other types of intruders as more damaging and dangerous.
No doubt, hackers working individually or in concert with others wreak havoc in the marketplace. Demchak notes the cost of such internet fraud at $130-billion to only six major corporations in 2010. A staggering sum. But even that pales in comparison to the damage that could be done if a nation with a sophisticated cyber war capability would fully implement these tools against another country.
In fact, Leon Panetta, in his first speech ever on “cyber-policy” invoked 9/11 and Pearl Harbor in warning of the danger of a cyber-attack on the U.S:
…[He] spoke in unprecedentedly stark language about potential military responses to cyber-attacks that threaten national security.
The United States is now in a “pre-9/11 moment,” Panetta said, at risk of crippling online attacks against public utilities, trains or chemical factories…[Such] attacks…could spark the “cyber Pearl Harbor” that the defense secretary has often referred to.
“An aggressor nation or extremist group could use these kinds of cyber tools to…derail passenger trains, or even more dangerous, trains loaded with lethal chemicals,” he said “They could contaminate the water supply in major cities, or shut down the power grid across large parts of the country.”
The most damaging attacks could combine a multi-pronged attack: knocking civil and military computer systems offline, with a physical attack on the country.
The defense secretary says the U.S. has, in response, developed the capability to trace such assaults back to their source and even pre-empt such attacks:
“Conventional wisdom about cyberspace right now is that it’s impossible to attribute attacks to any specific individual or nation-state, [but] we have invested a lot in the [Defense] Department in developing that capability,” the official [Panetta] said. “And it has improved tremendously.”
These are extraordinary claims which, if true, mark new developments in the field of cyber-war. Though, like many such official claims, they may be overstated in order to deter would-be enemies. They will need to be tested in the real world before we can determine how much is bluster and how much truth.
Returning to Demchak’s article, while he mentions Stuxnet as an example of such cyber warfare, he neglects to say that individual hackers or bad actors didn’t create this tool. Two states did. They did so not for any of the reasons Demchak mentions in his article. They attacked Iran to pursue interests of state. That means it is only a matter of time before one nation unleashes the full power of these weapons against another.
Images of the horrors of war are common from the news media: pictures of the wounded or the dead, buildings toppled, smoke plumes rising over devastated landscapes. What is especially insidious about cyber warfare is that it is often undetected. There are no bombs, no screaming fighter jets, and no military heroes. The enemy has no face, leaves no fingerprints. There are instead streams of code, exploits and hacks. The damage could be done before you even knew what happened.
These weapons, once unleashed against an enemy can easily turn around and bite us in the rear end. Chevron has acknowledged that its own industrial command systems were infected by the Stuxnet virus. They did no damage—this time.
A Chevron executive voices his concern:
“I don’t think the U.S. government even realized how far it had spread,” he told CIO Journal. “I think the downside of what they did is going to be far worse than what they actually accomplished,” he said.
A Wall Street Journal report quotes a computer security specialist on the Pandora’s Box effect of Stuxnet:
The tacit acknowledgement by U.S. government officials that they created Stuxnet makes U.S. companies an even bigger target, said Paller at SANS. He says hackers last summer went from stealing information to using cyber attacks to cause destruction. Stuxnet “opened Pandora’s box,” he said. “Whatever restraint might have been holding damaging attacks back are gone.”
Saudi Arabia’s national oil company, Aramco, suffered the most damaging commercial cyber-attack ever, which destroyed virtually all its employee PCs (30,000). Yesterday, the company acknowledged the ultimate aim of the attack was to sabotage oil production. Before this attack, which many believe may be attributed to Iranian interests, Iran’s oil facilities were attacked with a similar cyber-assault.
Demchak suggests that among the means societies should use to frustrate such cyber-attacks are preventive attacks (he uses the rather euphemistic term “disruption”) on the enemy outside the “gates” of what he imagines as the cyber city-state. The only problem with his suggestion is that the shrouded face of cyber-attackers rarely makes it possible to pinpoint the specific identity of the perpetrator.
For example, if Iran sought to “disrupt” those who seriously damaged its uranium enrichment program what should it do? Should it attack the home base of the IDF’s Unit 8200? Or should build its own cyber war weapons to disrupt Israel’s nuclear program?
In fact, Iran is already doing so. The NY Times offered a comprehensive analysis of the most massive cyber-attack ever on a commercial company, in which 30,000 computers of Saudi Arabia’s oil company, Aramco, were disabled. This took down the entire internal communications system of the company, though it didn’t harm oil production directly. Secretary Panetta’s speech is viewed as a veiled response and threat to Iran, which we view as the perpetrators of this attack.
The Washington Post reported that DOS (denial of service) attacks on Bank of America and JP Morgan Chase took down these sites recently. Review of the logs shows the origin was Iran. The article speculates that Iran was attacking U.S. banking interests because of the severe damage done to the Iranian financial sector by international sanctions.
Where does this end? It’s such a new game, we haven’t yet developed any rules. There are certainly no international agreements governing cyber war as there are regarding nuclear proliferation. Yet the stakes are so high, that precisely because there are no rules, someone may make a major miscalculation and drag an entire region into conflict.
In an otherwise thoughtful and suggestive essay, this is what’s missing from Demchak’s analysis. These bad actors won’t be, or won’t only be, Anonymous or Israeli-Russian hackers. They will be western democracies like our own, the very entities we’re so used to thinking of as the “good guys.” In cyber-war, the good guys could easily turn out to be the bad guys. Aren’t we finding that out regarding a U.S. president in whom so many of us placed so much hope? Champions of democracy could wield weapons that level broad swaths of enemy infrastructure. Then, who is right and who is good?
In fact, the Pentagon is opening a veritable Wild West of cyber warfare capabilities with its invitation to defense contractors to:
…Propose “revolutionary technologies for understanding, planning and managing cyber warfare.”
I foresee a massive expansion in use of what many might call cyber-terror and little control over where any of it may lead. While State Department lawyers argue that the laws of war apply to cyber-attacks, it gives me little comfort since these same lawyers are the ones who claim Obama’s kill lists are legally justifiable.
Unfortunately, we can’t return to the innocence of the birth of the internet. We can’t make human beings behave according to the “better angels of their nature.” But we can expose the bad actors when they are nation states (or individual hackers like Kras) and make them pay a price, however small, for trespassing the bounds of civilized discourse. We can call for international protocols governing the use of technology to pursue cyber hostilities. We can shame those who resist because it suits their own national or ideological interests to utilize cyber-terror for the interests of state.
Note: Kaspersky Labs, while deeply involved in cyber-security and protecting the Internet from hacking and cyber-attacks, takes no political position on the issues involved and does not attribute cyber-war attacks to specific national governments.
Related articles








Richard: You wrote: “Secretary Panetta’s speech is viewed as a veiled response and threat to Iran, which we view as the perpetrators of this attack.” Sorry to see the “we” there.
Maybe you are feeling that you are very American and that Panetta speaks for Americans.
My feeling is that Americans do not willingly and knowledgeably support America’s vast military empire or many of its (often secret) doings, and Panetta as the supervisor of all that (which is bankrupting the USA both morally and monetarily) is not a representative of America (at least not of the American people) but is a representative of the BIG-MONEY OLIGARCHY that actually runs the USA for its own interests (not necessarily those of the American people — witness the fall of the middle class over 20 years as the very wealthy, including the oligarchs, got fat and got powerful).
Point well taken. Sometimes that “we” just creeps into things when I’m speaking of things connected to the U.S. I even sometimes want to say it concerning Israel though I step back in doing so, realizing I’m not Israeli.
Excellent article, Richard. You are doing a tremendous service exposing the unfathomable dangers of the new cyber-universe where humans of all stripes are at the mercy of actors – private and government – benevolent and mafeasant – not held to any account whatsoever.
Unfortunately, the dangers of Stuxnet-like viruses becoming relatively commonplace (which is bound to happen, sooner or later) are not yet fully appreciated. With nanotechnology making the strides it does, with computer – and even iPhone- controlled implantable devices in progress (a huge favorite of ongoing DARPA projects, both open and less so), with robots running entire factories, the blurring of the human-cyber interface is about to be a fact of life. Just one small example: how long will teenagers addicted to their streamed music rolls and living within a “chat universe” tolerate having the limits imposed by hand dexterity and external microphones? there are companies already working on “embedding” of the digital into the biological (Here’s just one company to look at – Proteus, working on embedding electronics into pills).
With continuing shrinkage of the electronics boards, as more can be crammed into less, software will be the new tool of the 21st century, and as software will become more integrated with biological systems (including the human brain) the potential for direct physical harm will increase exponentially. Imagine what hacking into an implanted pace maker or an artificial limb can do. Or into an “embedded’ ear piece (which is what I expect will be coming along by and by). Or the damage that a virus can do not just to a computer or a machine but to a living breathing human.
I think some day, articles like yours and the ones you cite will become standard fare reading – to illustrate that there were those who understood the monumental dangers ahead of us, long before it became a common MSM refrain (MSM – always the last to figure things out, it seems – give or take a few).
Interesting essay but it is a pity that it has to derive part of its interest from your personal trouble.
I remember a comment by the Dutch historian Jan Romein that the relatively sophisticated financial management of the Roman legions initially gave these an advantage over their enemies but ultimately led to a “retarding lead”. When this financial management got into disarray these legions were at a disadvantage compared with their much more primitively organised enemies.
Wouldn’t the same kind of thing occur in the cyber wars? The states least dependent on computerisation (but provided with a mercenary team of excellent hackers) will be at an advantage.
This has no direct relevance for your own case Richard. Talking about that: what struck me was that as soon as your website was in a state of transition and thus vulnerable you were hit. This seems to imply that you were more or less permanently targeted by the miscreant who was waiting for his chance. What conclusions, if any, did the IBM Security Team come to?
I have two thoughts about this interesting article. First, this is the sort of issue that can be hyped in order to close down internet freedom as we know it. I’d worry about that as much as about cyber-war. Second — we need to remember that software doesn’t actually do anything, that is, it just manipulates data of a certain form. Software will not clean my porch or build a highway. Software cannot build real bridges, move households across country, bale that cotton. And information is only powerful if it is correct — corresponds in some way to the real world. Sure, we are dependent on computers to do its manipulations quickly and accurately, but how dependent? You can destroy a civilization by drying up its water resources, but can you do it by denying it information? I doubt it. Maybe the answer to cyber attacks is simply redundancy.
Of course Kaspersy has a political position. They are a KGB outfit.
@PP206 And you’re a Trappist monk.
what?? say it aint so
if I were IBM I’d be a bit worried what this Cras [sic] guy may have incognito-type put in the IBM technology and what IBM secrets he may be willing to sell to the highest bidder of give to Israeli interests.
Here’s hoping the criminal activity will be prosecuted to the fullest extent of the law.
Taking down your site is dead wrong.
However I find your broad accusations compared to some clumsy two pence hacker wrong as well.
I dont know who hacked your site, but it somehow does not look like the guy you found his email within the hack.
Imagine the police finds the thiev business card. It is too stupid even for the most stupid of them.
If he expected never to be exposed then of course he would’ve taken the chance of using his real e mail address. Especially if the hack was spontaneous and not something he planned out in advance. He would’ve gotten away with it if Kaspersky hadn’t gotten involved and there was no way he could’ve known they would.
So this was a case of hubris on his part and luck on mine that the good guys were on my side and helped exposé him.
In another form this article deserves wider publication. In my personal activities I maintain a data base concerning subnational attacks on the energy sector, worldwide. The computers on which this data base resides have never been connected to the Internet and it is unlikely they ever will be: a decision I made in the late 1980s. There are costs associated with that that I recognize and am willing to bear.