Sheldon Adelson’s Sands Resorts websites were hacked around the world yesterday (Tuesday). The corporate e-mail system was also taken down, and on one of the company sites a map of the world featured the locations of company resorts in flames. It also featured a picture of Adelson shoulder to shoulder with his political protegé, Bibi Netanyahu. On the same screen, the e-mail addresses and social security numbers of employees scrolled by. The hackers, calling themselves the “Anti-WMD Team,” also featured this message:
“Damn A [Adelson], don’t let your tongue cut your throat. Encouraging the use of weapons of mass destruction, under any conditions, is a crime.”
This referred to a panel discussion several months ago at Yeshiva University in which Adelson advocated dropping a nuclear bomb on Iran. A Sands spokesperson said that Adelson’s comments that night were “hyperbole.” Not sure what that means: did he only mean we should drop a conventional weapon on Iran like one of those 30,000 lb. bunker busters?
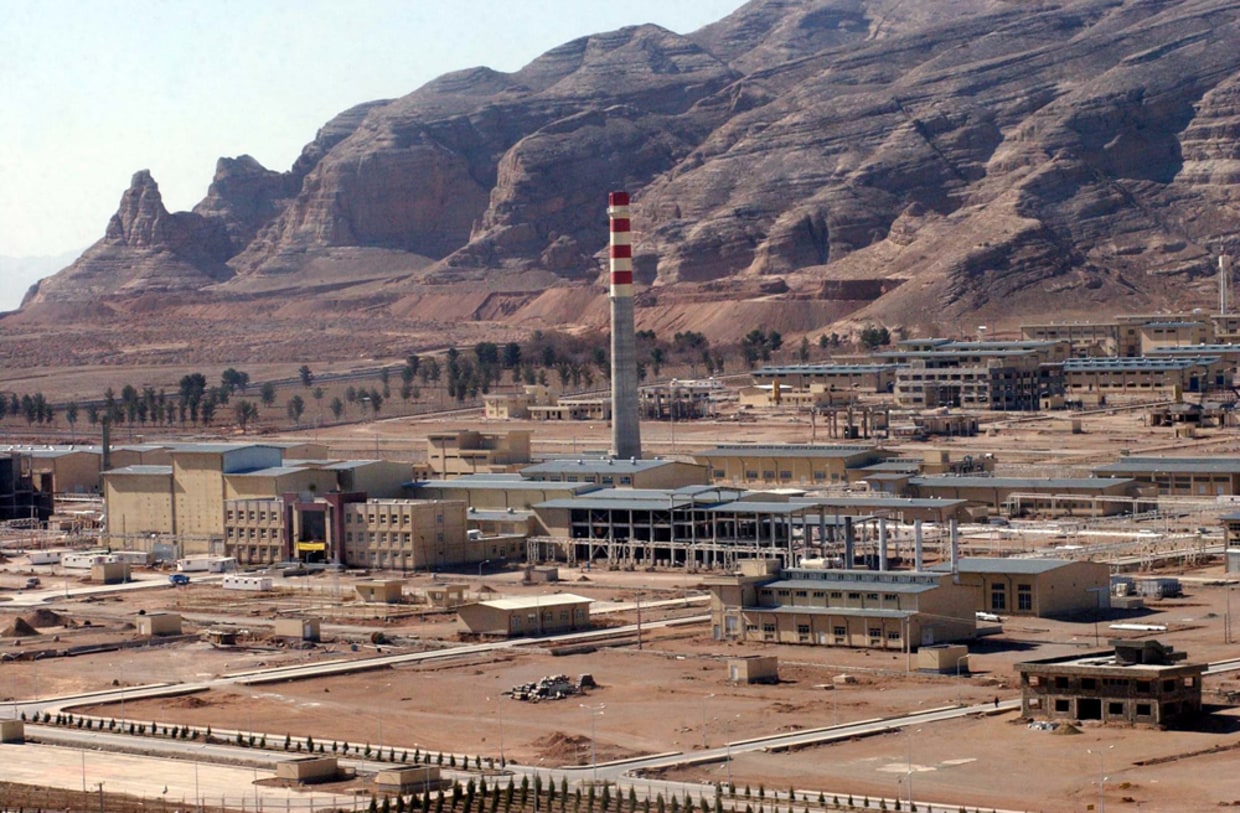
There are several suspects that should be considered. Perhaps the most obvious one is Iran. They have an active cyber-warfare capability and in the past year or two are believed to have attacked U.S. banks and Saudi Arabia’s national oil company, Aramco. Though Iranian cyber-sabotage would be highly sensitive given the nuclear talks underway with Iran and the west, attacking Sheldon Adelson, a harsh foe of both Iran and Pres. Obama, wouldn’t engender much ill will among U.S. Democrats.
Further, the veiled threat, “don’t let your tongue cut your throat,” was definitely not written by a native English speaker. In fact, Prof. Muhammad Sahimi, a native Farsi-speaker, wrote this to me:
“In Farsi we have a proverb: Do not let your tongue cut your head [off] (which obviously would be through the throat!)”
The other possibility is that this is an example of corporate sabotage by an enemy of Adelson’s Sands casino conglomerate. The article mentions that Adelson has come out strongly against online gambling (as a natural threat to his gambling empire). There certainly could be many interests that would want to take the Las Vegas tycoon down as he’s undoubtedly prepared to spends tens of millions to defeat such a venture.
What’s most interesting about this incident is that if it turns out it was politically motivated, it would be the first instance I can think of in which hackers attacked a specific corporate mogul for his political views (rather than his business practices). It’s also significant in light of Israel’s cyberwar campaign against Iran, in which it attacked that country’s nuclear facilities and assassinated its nuclear scientists. It’s not hard to imagine that this history combined with Adelson’s visceral hatred of Iran would motivate Iranian hackers to take action against him.
It may mean that Adelson has to turn to his pal, Bibi, and recruit some Unit 8200 alumni to spruce up the Sands cyber-defenses. It sounds like Sheldon didn’t realize that advocating a nuclear attack on another country might have a serious impact on the corporate bottom line.
A year ago, the Israeli police, and customs system computer networks were also hacked and brought down. The IP addresses used in the attacks were traced by to networks based in Gaza and the West Bank, though the hackers had targeted Palestinian victims before they turned to attack Israelis. Israeli officials leapt to the immediate conclusion the hackers were affiliated with Hamas, but this makes little sense since the Islamist group isn’t known to use cyberwarfare tools.
But this passage helps us identify a more likely culprit:
“When it comes to the Middle East hackers, they have obviously expended less effort in making their own stuff, and tend to rely on off-the-shelf tools, such as Blackshades, XtremeRAT and Dark Comet,” he said. Indeed, researchers have documented numerous examples of these commercial tools being used in espionage attacks against activists in other countries of the region, most notably Syria.
I consulted a computer security specialist who told me he thought it was much more likely the hackers were affiliated with the Syrian Electronic Army, pro-Assad loyalists. Such operatives have been active over the past year and attacked various targets around the world. Given that Israel has attacked Syrian military assets at least five times over the past year, targeting some of its most advanced, Russian-made weapons, the regime has all the reason to attack Israeli cyber targets. In fact, it’s even possible that Syrian and Iranian hackers may be working in concert since both countries are allied in fighting the civil war in Syria.
Last month, another similar attack targeted the Israeli defense ministry, including computers of the Civil Administration, which maintains the Israeli Occupation of the West Bank. Other compromised omputers were used by Israeli defense contractors who “supplied defense infrastructure.” Israeli cyber-analysts again blamed Hamas saying the attack was similar to the one mentioned above. This exhibits the typical Israel hubris of seeking an explanation that accords with its prejudices and pre-conceived notions, instead of evidence. It is a lot easier to blame Hamas since they are the perennial punching bag. But Israel has never acknowledged that Syria, a much more powerful enemy might be attacking its security cyber-infrastructure. That would cause a lot more alarm within Israel.
Also, given that Israel has targeted some of Russia’s most sophisticated weaponry in these attacks, that country would also have reason to want to spy on Israel’s defense ministry computer network. Russia, Iran, and Syria are all allies in the civil war, as I mentioned above.
This passage suggests inconvenient timing for the Israeli prime minister:
Word of the cyber attack came a day before a three-day Israeli cybertech conference being held in Jerusalem, and just after Prime Minister Benjamin Netanyahu plugged Israeli technological advances at the World Economic Forum in Davos.
At the cyber-conference mentioned above, there were Israeli cyber-security companies hawking their wares to corporate and government customers. Many of these companies’ products were developed by programmers who’d only a few years before created the very threats from which they were now defending, when they served in the IDF’s cyber-warfare group, Unit 8200. It’s the height of cynicism for a country to create some of the most potent cyber-war tools in the world and then to exploit this by creating defensive measures to protect against them.
It reminds me of the burglar network which conspired with the local security companies both to break into people’s homes, then sell them locks and security systems to protect against the attacks. Not to mention that when the security system is installed, the company knows its vulnerabilities and can allow the robbers back in to plunder the home again. That, in short, is Israel in today’s cyber-security world.
This portion of Bibi Netanyahu’s speech at the conference sounds especially chilling when you consider that Israeli hackers, working on behalf of the Israeli government, have created some of the chaos he warns against:
The concept of privacy, the prime minister said, was antiquated – or at least different than it used to be. “The networks are exposed. The fact that we have networks, increasing complexity of networks, interconnectivity on networks means that anything and everything can be exposed. The Internet of everything means that everything can be violated,” said Netanyahu. “The whole idea of intellectual property – that is being fundamentally challenged. The privacy of individuals – fundamentally challenged. The sanctity of our bank accounts – fundamentally challenged. And this goes obviously into public systems: power grids, traffic nets, water systems – you name it. Everything can be violated. Everything can be opened up. Everything can be also sabotaged.”
Given that Israel is guilty of every such sin enumerated above, why would anyone trust an Israeli company to protect us from such threats? Why would all those American companies rushing to invest in Israeli cyber-security startups do so when their own products could end up compromised by their own Israeli employees either by creating them or informing Unit 8200 about their vulnerabilities?





Last year in April: Anonymous launches coordinated cyberattack on Israel.
Recent announcements by hackivist group for cyberattacks on Israel in 2014 – Parastoo on Syria, Terrorism and Israel.
The release of intercept of Nuland’s conversation on regime change in Ukraine was done through an Anonymous website.
Wasn’t me.
OFF TOPIC NEWS ALERT for Richard – (please don’t post under this article)
Mr Silverstein, please immediately see Haaretz and Mondoweiss.net – Netanyahu just attacked EU President Schultz for saying Israelis 70 liters to Palestinians 17 liters.
Knesset walkout on Schultz
Richard – could this possibly be ‘IT’ for Netanyahu? – can he and Apartheid be destroyed over this?
I understood only the Bennett faction walked out because of “German lies.” Martin Schulz, a frontrunner to succeed José Manuel Barroso in Brussels, is quite a controversial figure during his years in EU parliament. If this incident helps him lose the race, it will be a win-win event.