 Calcalist published (English language report) a shocking story yesterday revealing that a secret police unit employed NSO Group’s Pegasus spyware against a diverse group of Israeli citizens. It did so without a warrant or any form of judicial review, as is characteristic in these situations. It first purchased the technology in 2013 with a contract worth $700,000. It undoubtedly paid millions more over the following eight years:
Calcalist published (English language report) a shocking story yesterday revealing that a secret police unit employed NSO Group’s Pegasus spyware against a diverse group of Israeli citizens. It did so without a warrant or any form of judicial review, as is characteristic in these situations. It first purchased the technology in 2013 with a contract worth $700,000. It undoubtedly paid millions more over the following eight years:
…The police purchased the software’s most basic form, and additional upgrades were added to it at costs of millions of shekels each year for the development and operation of the software.
Among those hacked were leaders of the Black Flag protest movement demanding the resignation of “Crime Minister,” Bibi Netanyahu. Also, a mayor was hacked in hope that access to his phone would reveal his participation in a bribery scheme. No legal action was ever taken against the municipal official. In some cases, the police hacked phones not because they had evidence of wrongdoing, but engaged in a fishing expedition, hoping they could dig up dirt via the phone break-in.
In essence, Israeli citizens accused of no crime were spied upon by the national police. They included government employees and anti-LGBT activists after the murder of a young girl attending a Pride march. Though the police claim that all their activities are overseen and approved by the attorney general and police minister, that seems doubtful at best. So far, neither has admitted knowing of this activity, let alone that they approved it. But given that this is Israel, and government officials lie through their teeth when it’s convenient, it’s very possible that either they knew or that they looked the other way.

Secret Police Unit Used Pegasus to Dig Up Dirt on Closeted Social Media Activist
Pro-Israel advocates like to call Israel a gay oasis and compare it favorably to the homophobia of neighboring Arab countries. This, of course, ignores flagrant acts of murder and violence against the LGBT community in Israel. In fact, a homicidal Haredi Jew who stabbed a gay man at a Jerusalem pride rally served 10-years in prison. When he was released, the police lost track of him and he pounced once again at a Gay Pride march. This time he stabbed a young woman to death.
So you won’t be surprised to learn that an unnamed social activist came to the attention of the police for reasons that remain unclear. The man was married, but used the Grinder app to conduct surreptitious affairs with gay men. The police infected his cell phone with Pegasus and learned about his planned trysts. Pegasus exposed all of this secret, private data to the cops.
Using it, they assigned field units to tail him to these assignations. The field units were not told what the subject had done; nor were they told where the intelligence had come from which led him to fall under suspicion. Only after the secret intelligence was gathered did the secret unit tell its colleagues to obtain a judicial warrant to tap his phone. The colleagues themselves had no idea where the information on which the warrant would be based originated. The reason given for investigating this particular subject? He was married and had affairs with men.
Contrary to police claims, they were fishing and looking for suspects and hoping to find criminal activity. That’s why they never filed for a judicial warrant: they couldn’t reveal to a judge why the suspect was targeted, because there was no legitimate reason.
When Calcalist asked the police why he was hacked and tailed they replied that they suspected that he would “commit grave offenses against public order.” They believed, in words that defy belief, that he constituted a “danger to democracy.” What is more dangerous to society? A closeted gay man or a secret police force running roughshod over privacy rights of innocent citizens? It suspected that he might commit a crime, though it had no evidence that he would. And it used Pegasus in the hopes dredge up some intelligence that would constitute a crime that they could pin on him. Instead, they discovered that he conducted a closeted gay lifestyle, which is by no means a criminal offense. So why did they bother to trail him to his trysts? What crime did they expect he would commit there?
After the police were notified about this particular Calcalist report they complained that the incident in question “was not familiar” to them. And that details which would permit it to investigate were deliberated omitted from the story (in order to protect the victim’s privacy of course!). It invited the media outlet to convey such information to them so that it could mount such an investigation. Yes, they said this with an apparently straight face!
The protocols used by police in this context were first developed by the IDF Unit 8200, the infamous SIGINT cyber-intelligence squad, which engages in massive spying against Palestinians in order to probe personal weaknesses which might offer opportunities to recruit victims as Shin Bet informants. There are no constraints on the hackers in this unit. They can do what they want when they want. The only thing that matters is digging up dirt which can be exploited to turn innocent Palestinian into snitches.
These are the same hackers who later joined the police SIGINT unit in question. Many were recruited by the former Shin Bet chief, Roni Alsheikh, who saw first-hand the benefits of secret surveillance technology in the spy agency’s own work. Unit 8200 veterans in effect, transferred to their new assignment the same mindset they used in victimizing Palestinians, but now targeting innocent Israeli civilians. Thus, the travesties perpetrated by the Israeli security apparatus against Palestinians later infect Israel itself. The Occupation is not, as most Israeli believe, “out there.” It is, as Stokely Carmichael said about the JFK assassination: the “chickens coming home to roost.” In other words, the Occupation-is-us.
The Ghana Connection
Now for a more conventional NSO violation of privacy rights: Israeli Chanel 13 has discovered a new country which was previously not known as a client of the cyber-spyware company: Ghana. In 2015, at a nondescript apartment near the beach, nine Israelis worked assiduously to install Pegasus on behalf of the country’s intelligence ministry. They also trained Ghanaian personnel how to use the technology to hack the devices of their targets. The apartment had no connection to the national intelligence agency, but was owned by the country’s national security advisor, a close confidant of its president.

The contract between the two parties was signed several months before national elections and the purpose of the transaction was to spy on the opposition. This was quite similar to the sale of Pegasus to the Ugandan intelligence services just before that country’s elections. Pegasus was operative in Ghana for over a year. NSO’s business ended there after a business dispute arose with Ofong.
Though the company has responded saying it has never operated spyware in Ghana. This seems a bit of disingenuousness. Of course, the Ghanaians operated it. But they could not have done so without the technology itself and the training provided: all by NSO.
At a later stage in the reporting of the story, NSO changed its story, telling Channel 13 that it had supplied Pegasus to Ghana, but that the deal had been canceled before the equipment was operational when it discovered that the spyware was intended for use in a manner that violated the ethical norms of the company. If you believe that, I have a bridge to sell you in Brooklyn.
The purpose of the spyware purchase: to monitor the opposition. Keep in mind that Ghana is considered a stable democracy, especially by African standards. It holds elections regularly and there have been transfers of power from one party to the opposition over the years. So one wonders why the current leaders found it useful to invade the privacy of their opponents.
Channel 13 also has the $5.5-million contract signed by NSO with Ghana. NSO’s local agent was George Ofong, It did not sign the contract itself. Rather Ofong did. Thus allowing the company plausible deniability in maintaining that it has not done business there. It followed this arrangement in many countries in which it did business. In many cases including Mexico, this permitted NSO to slip millions in bribes (aka commissions) to the putative clients and its own middlemen. In Ofong’s case, he and his associates took a cool $2.5-million commission, nearly half the value of the overall contract.
After the elections, the opposition did indeed win and assume control of the government. It in turn approached a different Israeli Cyber-security company, Megiddo to supply similar services. However, a scandal arose when senior government officials were discovered pocketing hundreds of thousands of dollars before services were even rendered.
One thing is for certain: NSO, and by extension Israel, played a key role in sabotaging democratic values and the rule of law in yet another democratic nation. Yet another reason to outlaw this potentially lethal technology.
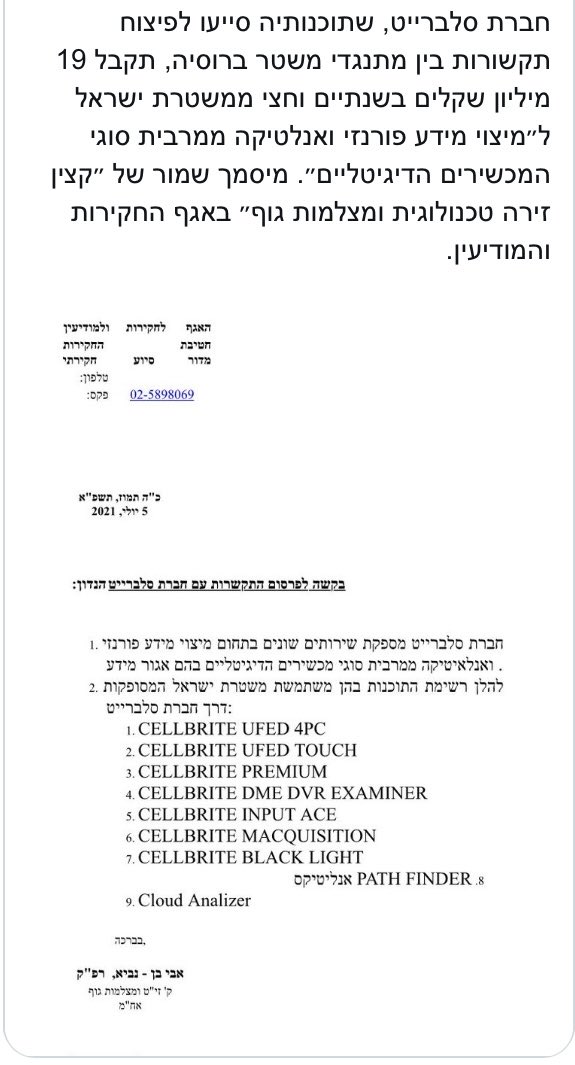
The Cellebrite Connection
Nor was NSO alone in offering the police tools to victimize Israelis. Cellebrite’s UFED technology extracts the contents of cell phones when clients have direct physical access to them. Like NSO, Cellebrite was used to hack the phone of a leader of the Black Flag movement, despite the victim never having committed a crime. Police sought to intercept messages between organizers in order to know their plans and interdict or sabotage them.
The national police chief declared that these activities were done with the approval of the judiciary. Nor were they used against “innocent citizens.” This contradicts the reporting about NSO, which notes there was no judicial oversight over its use in criminal investigations. Cellebrite responded to the report:
‘What do you mean “break-in? We work with law enforcement. We do not do it anymore but it depends on the situation. We work with the police, everything is fine, everything’s cool.’
The company just signed a contract valued at $4.5-million over a two-and-a-half-year period.
Even more sleazy is the cozy relationship between the police and private hackers, whom it employs as subcontractors to break into the cell phones of its targets whom it has failed to access. The police cyber unit employed at least three of these individuals much like China and Russia does, distancing law enforcement from activities which might embarrass it. These hackers have no security clearance, nor was a background check performed to determine if they have a criminal background. They had no police training though they are privy to the most personal information and secrets Israelis maintain on their private electronic devices. They could easily have taken advantage of their access by blackmailing the victims or selling the information via the dark web. Indeed, one of the hackers had been sued by Sony in 2015, accused of setting up a website which sold the internal code of Playstation 3 for the paltry sum of $20.. It allowed users to download many Playstation video games for free. After the police recruited him, his fortunes changed dramatically. In some months, he was paid $12,000 for his hacking skills.
The police neither requested nor received judicial approval for these hacks.

One of the many ironies of this incident is that the police chief who made most extensive use of NGO’s spyware was Roni Alsheikh. He had come to the police from the Shin Bet, where he’d been the deputy director. In a separate case, the Shin Bet has recently been accused of hacking into the phones of the PA foreign minister to track its collaboration with the ICC’s war crimes investigation of Israel. This of course raised barely a ripple inside Israel, because offenses concerning Palestinians, even ones perpetrated by Israel, arouse no interest.
Another irony: an Israeli TV news report found that cronies of Bibi Netanyahu, then under police investigation regarding corruption charges, had employed security consultants (i.e. spies) to target the police investigator and discover what they knew, and what approach they planned in questioning the PM. Thus, while the police used Pegasus to target Israelis, the PM’s allies were using similar methods to spy on the police themselves. Ironies abound…
The use of NSO’s malware hammers another nail in the company’s coffin. It already has been placed on a US black list which prevents all US financial institutions from funding any corporate transactions. This also would discourage any potential US clients from purchasing its products. Though the company previously avowed that its spyware did not spy on Israelis, it released a new statement which did not deny it was used in the fashion alleged. Instead, it used an old deflection, claiming it has no control over the ways in which clients use its products. This is of course a lie. If NSO wished to oversee use of Pegasus it could build into the system a means of reviewing practices which violated terms of its contracts. It chose not to do so in order to give itself plausible deniability in circumstances just like those it faces now.
The new element introduced in the current scandal is the use of the malware against Israelis, who are much less troubled by its use against foreign targets. Domestic use hits much closer to home and arouses outrage not seen previously. But will the incident raise hackles sufficiently to force change in NSO’s methods? Will it pressure the government to apply more stringent regulatory measures to limit its right to invade the privacy of Israeli citizens, not to mention the tens of thousands of foreign victims of its technology? Will it lead in the long run to a global ban on this lethal technology as Edward Snowden demands? All this remains to be seen.
Police NSO Scandal in Context of Overall Deterioration of Israeli Rule of Law
Though one should not be surprised I am–regarding the status of national police chief, Kobi Shabtai. Why does he still have a job? Why has no one, including the government or opposition, called for his head on a platter? That this hasn’t happened testifies to the absolute and unchecked power of the security apparatus. No doubt these politicians are cowed by the fact that the police have dirt on every one of them. Possibly collected by Pegasus itself.
While this scandal is in itself deeply disturbing, it is more important to place it in the context of the deterioration of the rule of law. As it is, the judiciary is a rubber stamp of the police and security apparatus. They are incredibly pliant to demands made upon them. They bend themselves into pretzels to accommodate every demand and request. So why did the police decide to forego even the flimsiest oversight? Probably because they knew that they could not get approval from judges for these expeditions. Given the wide latitude given to the police by them, it’s astonishing to realize even they would not go that far. There are limits to their gullibility, as generous as they may normally be.
Further, this spy scandal reveals the corruption and lack of accountability at the heart of Israeli society and governance. Prime ministers arrange for corrupt billion-dollar submarine deals with tens of millions changing hands under the table (one of the hands belonging to a Netanyahu lawyer). Netanyahu is the second prime minister accused of such corruption (Ehud Olmert was convicted and served prison time). If convicted, Netanyahu would be the second PM to serve prison time. The plea deal reported in Israeli media would offer the PM no prison time and a modest slap on the wrist. While it would prohibit holding political office for seven years, it would not prevent him from pulling all the Likud strings behind the scenes. He would certainly maintain control of the Party through appointing his cronies to key leadership positions.
In other words, in every major sector of government from the security apparatus (including the military) to the political echelon, senior officials do as they wish, without regard to norms. They defy any precedents. They defy rules or conventions established over decades of practice. They invent ever newer ways of evading regulation or accountability.
As a popular saying from the realm of coding declares: this is not a bug but a feature.





Richard said:
“They included government employees and LGBT activists after the murder of young girl attending a Pride march ”
In fact, anti-LGBT activists were hacked.
“The police also seem to have used Pegasus for general intelligence collecting, such as using it to spy on potentially violent anti-LGBTQ activists after the 2015 murder of a young girl at Jerusalem’s Pride Parade.”
https://www.haaretz.com/israel-news/police-used-nso-s-pegasus-to-spy-on-israelis-without-court-order-report-says-1.10546407
C’mon Richard.
@ Nate Depp:
Hasbara 101: avoid attempting to rebut the major argument offered by your opponent. That’s often a losing proposition. Instead, focus on minor discrepancies or errors which [you hope] will raise doubts in readers about the overall credibility of the argument offered. A losing proposition as well.
It’s a cheap trick. I will review the sources I used in writing the article.
I haven’t attempted to rebut anything, because I think this abuse of police power is scandalous.
I agree with Yankel’s comment, below, adding that Israeli apathy will only make this bad situation worse.
Trust me. I won’t bother fact checking you again.
@ Nate Depp: Just to be clear, I don’t mind fact-checking. In fact, I welcome it & people have pointed out such errors in the past (thankfully, not too many!). I just don’t like gotcha fact-checking (ie “I caught you out making an mistake–nah, nah”). That posturing annoys me.
BTW, I did correct my error and thank you for pointing it out.
The REAL problem is that most of the Israeli Public don’t care they’re being spied on.
This I am uncomfortable with this part. It smacks of hypocrisy and double standards by the powers that be that single out Pegasus.
Facebook and Twitter, and other social media giants harvest data on US citizens. Is there anyone here that doesn’t believe that CIA have access to this data? I certainly believe the CIA uses data from social media firms for mass surveillance. Singling out Israel like this over Pegasus is unfair.
@ Anupam: Before calling out anyone else, you might want to explain why your Hindutva pal, Narendra Modi bought Pegasus to spy on his political opponents. Explain to me the secrets he exposed from the victims privacy rights and why he had any right to do this?
As for Facebook et al.: of course the amount of personal data it collects is unconscionable. And I support the regulation of what are in effect public utilities.
However in a strict sense, users have given permission for this data to be collected. These users may not realize they’ve given this permission. But by using the platform, they have done so. They’re entitled to stop using the platofm and the data collection will stop.
So your argument doesn’t hold up. But it was a nice try.
The CIA doesn’t need to harvest social media platofm data. They have the NSA to do that for them. And the NSA compiles far more data and is far more intrusive, according to Edward Snowden.